Critical Vulnerability: Cisco IOS Now Patch Available (CVE-2023-20198)
by Chris Gerritz
3 min read
Published: 24 October 2023
Last Updated: 24 October 2023
DEFCON-level vulnerabilities in Cisco IOS’s Web UI, which has resulted in tens of thousands of Cisco switches and routers hacked in the last month, has finally been patched (as of 23 Aug 2023).
Cisco IOS is the operating system of Cisco devices and its’ web User Interface (UI), if enabled, is being actively attacked with two major remote code execution (RCE) vulnerabilities (CVE-2023-20198 & CVE-2023-20273) that were first reported early last week. Over 140,000 Cisco devices are exposed to the internet and at least 30,487 devices and growing have been confirmed compromised so far.
Vulnerability Information
- Product: Cisco IOS XE Web User Interface (UI).
- Affected Versions: 17.9.3 and prior versions
- CVE: CVE-2023-20198 (CVSS 10.0) — Also related: CVE-2023-20273
- Type: Remote Code Execution (RCE) Vulnerability
- Disclosure/Publish Date: 16 October 2023
- Advisory: https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-iosxe-webui-privesc-j22SaA4z
- First Patched Version: 17.9.3a (22 October 2023)
- First Exploited: As early as 28 September 2023
- First Publicly Available Exploit: 17 October 2023
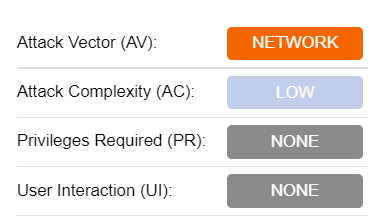
Description: This vulnerability allows a remote, unauthenticated attacker to create an account on an affected system with privilege level 15 access. The attacker can then use that account to gain control of the affected system at the highest privilege levels.
Note: Cisco IOS has multiple supported release trains depending on device type and your update schedule. 17.9 is the latest. If you run IOS versions 17.6, 17.3, or 16.12 (Catalyst 3650 and 3850 only), be on the lookout for updates soon.
Recommended Actions
Determine if the Web UI is Enabled (From the IOS Command Line)
The feature being exploited is called the HTTP Server (http server or http secure-server). You can determine if this is enabled by running the following commands from your Cisco device’s commandline interface (CLI):
> show running-config | include ip http server|secure|activeNote: If the name of either feature is returned from the system configuration, than the web UI feature is enabled.
Update IOS Versions

Block or Limit Remote Access to Cisco Devices
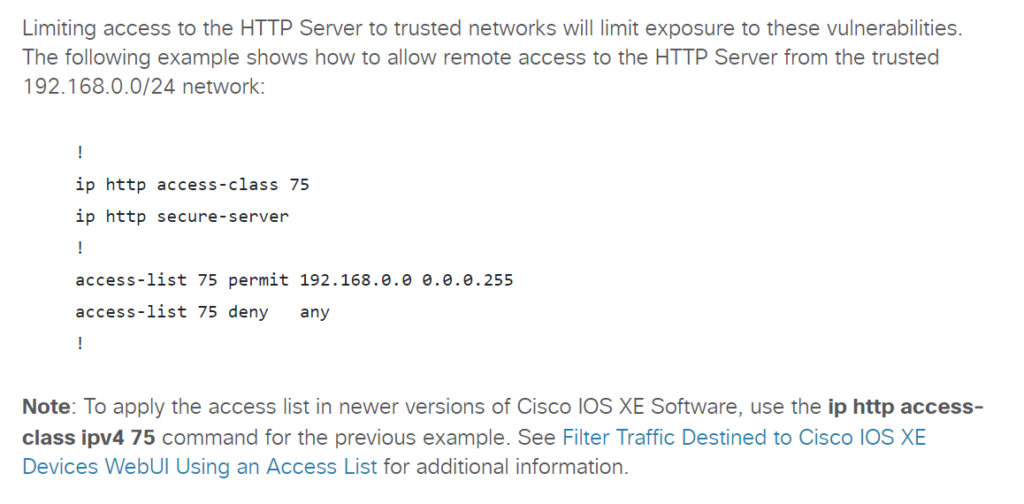
If enabled, ensure the device is not accessible from the internet or an untrusted subnet on TCP ports 80 and 443. Either disable the web UI feature completely or heavily restrict routing to this device on those ports.
Cisco provided guidance on how to limit access using an access control list inside IOS like so:
Audit IOS User Accounts on Suspect Devices
If you find an IOS device that was exposed to the internet or an untrusted network, look for any unfamiliar or new user accounts created in the last 60 days.




