Cisco FMC – RCE with No Auth Required
by Mike Puglia
2 min read
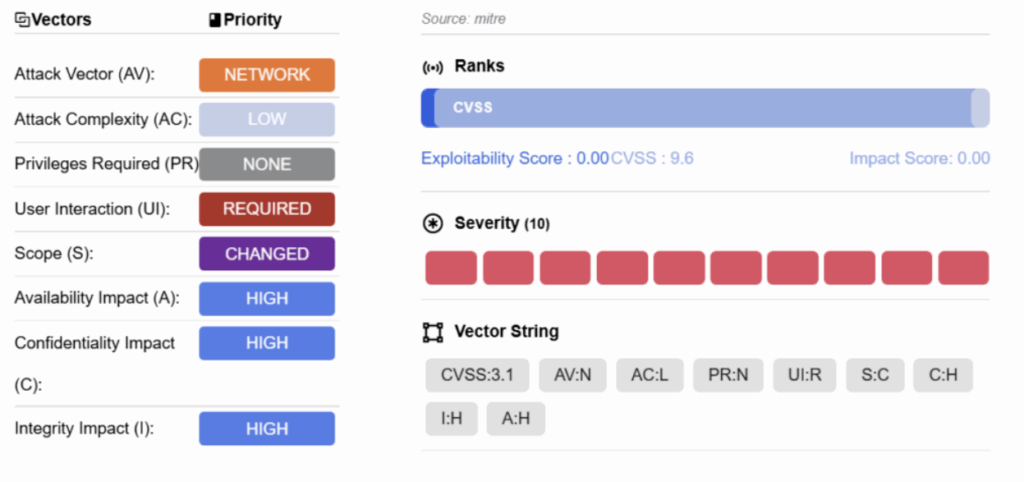
Cisco has published a critical vulnerability (CVE-2025-20265) with the highest severity score (CVSS 10.0) for its Secure Firewall Management Center (FMC) product. The vulnerability, a Radius Remote Code Execution Vulnerability, enables an unauthenticated attacker to remotely inject arbitrary code, typically shell commands, that are executed at with high level privileges. The flaw is present in FMC versions 7.0.7 and 7.7.0 and requires RADIUS authentication for the web-based management interface, SSH management, or both. Cisco’s internal team discovered the issue during testing and it has not seen exploitation in the wild.
Vulnerability Information
- Product: Cisco Secure Firewall Management Center (FMC)
- Affected Versions: 7.0.7 and 7.7.0
- CVE: CVE-2025-20265 (CVSS 10.0 – Critical)
- CVE Publish Date: 14 August 2025
- Type: Untrusted Search Path – leading to unauthenticated user to conduct an escalation of privilege via network access
- Advisory: https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-fmc-radius-rce-TNBKf79
Recommended Actions
Cisco has released free software updates that address this vulnerability and organizations should prioritize upgrading to the latest Cisco FMC version. If immediate updating is not possible, mitigate the vulnerability by switching from RADIUS/SSH to another type of authentication, such as local user accounts, external LDAP authentication, or SAML single sign-on (SSO). As a reminder, Cisco FMC should never have the web-based management interface exposed to the public internet.
Our Response
Datto EDR and RocketCyber Managed SOC both have deployed rules to detect shell processes spawned by FMC-related authentication or web processes such as radius clients, fmc-auth, nginx, httpd and others.